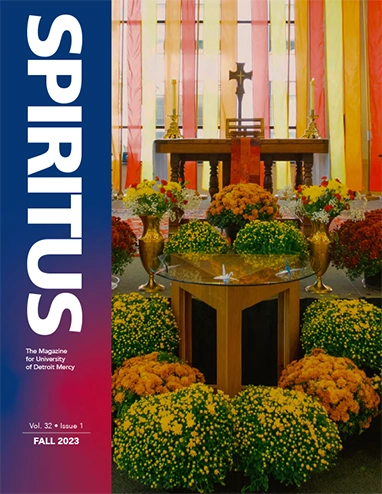
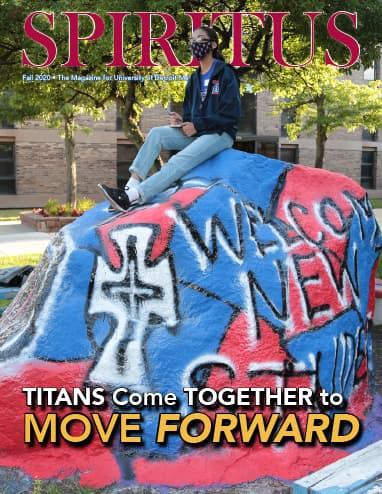
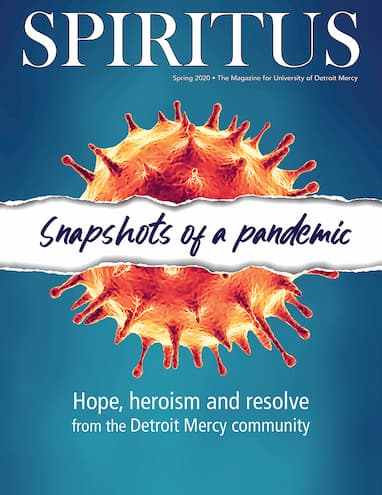
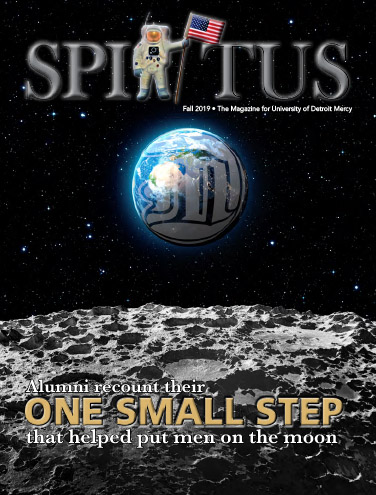
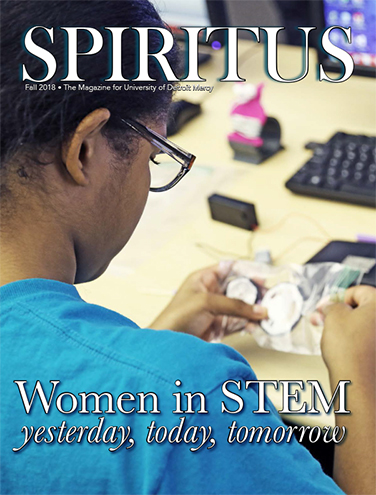
Spiritus Magazine
Spiritus. The University of Detroit Mercy Magazine highlights Detroit Mercy's past, present and future with a collection of feature articles, news, and alumni updates. All University alumni receive a complimentary printed copy of Spiritus twice per year. Class Notes and In Memoriam are also updated throughout the year on the Alumni Community.